When running a mission-critical Web Map Service (WMS) platform, it is important that you have full control over who can access your geospatial information. Particularly if your data contains classified information or needs protecting from inappropriate use due to commercial restrictions.
Carmenta Server has a built-in security system that can be configured to allow or restrict access to particular map services or individual layers for each individual user. This security system has been designed for simple integration with existing identity management systems, e.g. Active Directory or LDAPbased authentication servers.
Protecting geospatial assets
Geospatial information is a valuable asset for many organisations, and a considerable amount of time and effort has usually gone into to collecting the data and building up extensive and often unique geospatial databases. In some cases the geodata also contains sensitive information about objects or conditions and, more often than not, this geodata is intertwined with other, less vulnerable, datasets.
In military Command & Control (C2) systems it is, of course, crucial that only authorised personnel can see the geospatial intelligence layers, whereas all non-sensitive background maps can be accessed more widely within the organisation.
Specific security measures are necessary when setting up and maintaining control of sensitive geodata in a web service environment. Only users with certain privileges should be permitted to access classified geodata, whereas access for all other users should be restricted. Carmenta Server’s built-in security technology is easily configured and provides a highly secure method of controlling your geospatial assets.
Using the service interface, Carmenta Server filters out which map services can be seen by each client, based on their user privileges. Even access to individual map layers within a service can be restricted.
Diagram 1 below shows a simplified view of how this can be applied. Geodata sources with a mixed content of both open and classified data can be natively read by Carmenta Server, and then made available as web map services. The security system within Carmenta Server can be configured to only permit access to services and layers that match the user’s privileges.
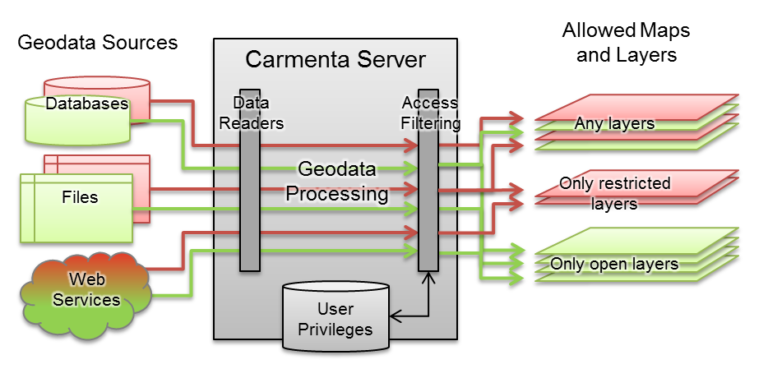
Diagram 1. Carmenta Server can restrict access to sensitive web map services and map layers.
Controlling who can use the data
Security in a web service environment relies on a few important elements. Authentication is the
unique identification of a user, whereas authorisation is the process of controlling which assets an
authenticated user is permitted to access.
Carmenta Server has an integrated single-sign-on solution (realm login) that can either be used as a standalone solution or be connected to various user and Active Directory (AD) or LDAP-based authentication servers. The security solution uses a central administration server process, which manages the login procedure for all of the Carmenta Server components. A flexible plug-in system enables it to be connected to various backend authentication servers, either locally or over TCP/IP. Diagram 2 demonstrates the relationship between the various components involved in the
authorization process.
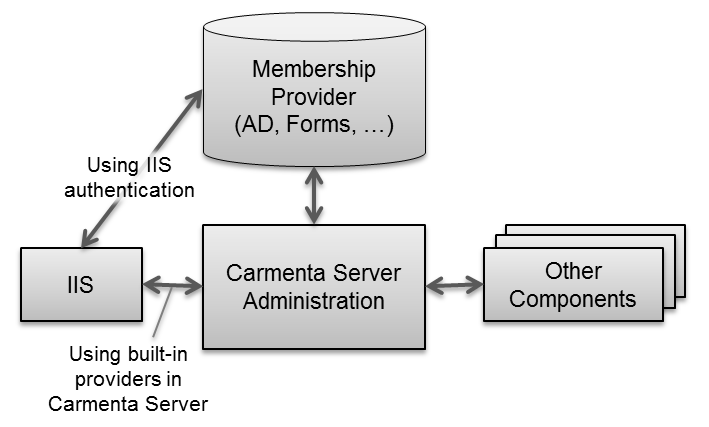
Diagram 2. A central administration process manages thelogin procedure for all of the Carmenta Server components.
Authorisation of authenticated users can be carried out in three ways, depending on the IT environment in which Carmenta Server is being used:
- Microsoft IIS manages the user login procedure via Windows Integrated Security, and checks user privileges against an Active Directory (AD). Carmenta Server then receives identity information via the Windows functionality.
- Carmenta Server manages the user login procedure directly via Windows Security, and only the Carmenta Server Administration component contacts the AD.
- Carmenta Server manages the user login procedure with Forms, and IIS is not involved at all.
Once the security system has been activated, login is required to access the map server, then all user requests will be checked against privileges and restrictions stored in Carmenta Server. Restricted maps and layers, i.e. data that the user is not authorised to view; will not appear in any capabilities or any of the web interfaces. Any requests to view or download restricted map images or data will generate the same error message as the one for a nonexistent layer. The built-in Carmenta Server TileStore cache has also been integrated into the security system, to enable usage but still prevent classified data from leaking out.
It is highly recommended that you disable all inactive web interfaces. OGC WFS and WCS interfaces are particularly sensitive, as they can provide access to the actual data and be used to download data from the servers. It is also recommended that you always use a firewall to block access to ports that are not being used for the web services. If a transparent web cache like Squid is being used, it is important that direct access to the web server is blocked, thereby forcing all requests through the cache.
Centralised configuration in Carmenta Server
User restrictions are easily managed and edited under Tools; on the web-based administration pages in
Carmenta Server.
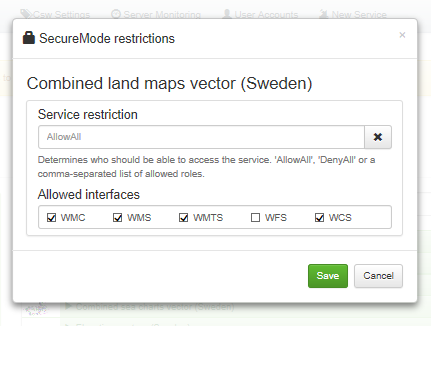
Diagram 3. Image showing how user restrictions can be managed.
Restriction options are either AllowAll, DenyAll or a comma-separated list of authorised roles. We do not recommend combining DenyAll or AllowAll settings with actual roles. All security settings are safely stored in Carmenta Servers and can only be edited by users with the right privileges.
Summary
Carmenta Server comes with a built-in security system that enables very precise control over how and by whom the geospatial data can be accessed. Geodata with different protection requirements can be managed in the same server, as Carmenta Server is capable of filtering services and map layers safely and on-the-fly, based on user privileges and restrictions. It can also be seamlessly integrated into an organisation’s existing security infrastructure.
Any organisation that provides access to geospatial information via web services would benefit greatly from Carmenta Server’s flexible security system. In addition to the product’s excellent stability and overall performance, it also comes with highly efficient, centralised administration tools that simplify the setup and maintenance of the security configuration.
Another important element worth remembering is that protecting valuable geodata assets is not just a technical issue; it also includes the routines and people involved in geodata management.